Privacy Architecture
At Himalayan Data Peak, our expertise in predictive analytics is built on a foundation of rigorous data integrity. This policy outlines how we handle personal identifiers with the same precision we apply to high-altitude research.
Input Specifications
We define our data collection boundaries strictly by the needs of professional engagement and technical research optimization.
Direct Communication Data
When you engage our consulting services via our contact forms or email (info@himalayandatapeak.digital), we collect your name, professional email address, and organizational details. This is necessary to facilitate predictive analytics proposals and project briefing.
Technical Telemetry
To maintain the performance of our digital infrastructure, our servers log standard HTTP request headers, IP addresses (obfuscated where required), and browser signatures. This data is used solely for traffic diagnostics and security monitoring in our Hanoi 19 operations center.
Research Metadata
For partners utilizing our data platforms, we record usage patterns to refine our predictive analytics models. This data is typically aggregated and stripped of PII (Personally Identifiable Information) before being processed for long-term insights.

"Information security is not a feature; it is the substrate upon which all predictive intelligence is built."
Data Lifecycle Standards
Purpose Limitation
We process data exclusively for the purpose specified at the time of collection. Your information is never sold to third-party brokers. We use your professional data to tailor our analytics research to your specific sector.
Retention Thresholds
Personal identification is held only as long as active consulting engagements persist. Archived project data is subject to anonymization protocols once the legal or contractual retention window expires.
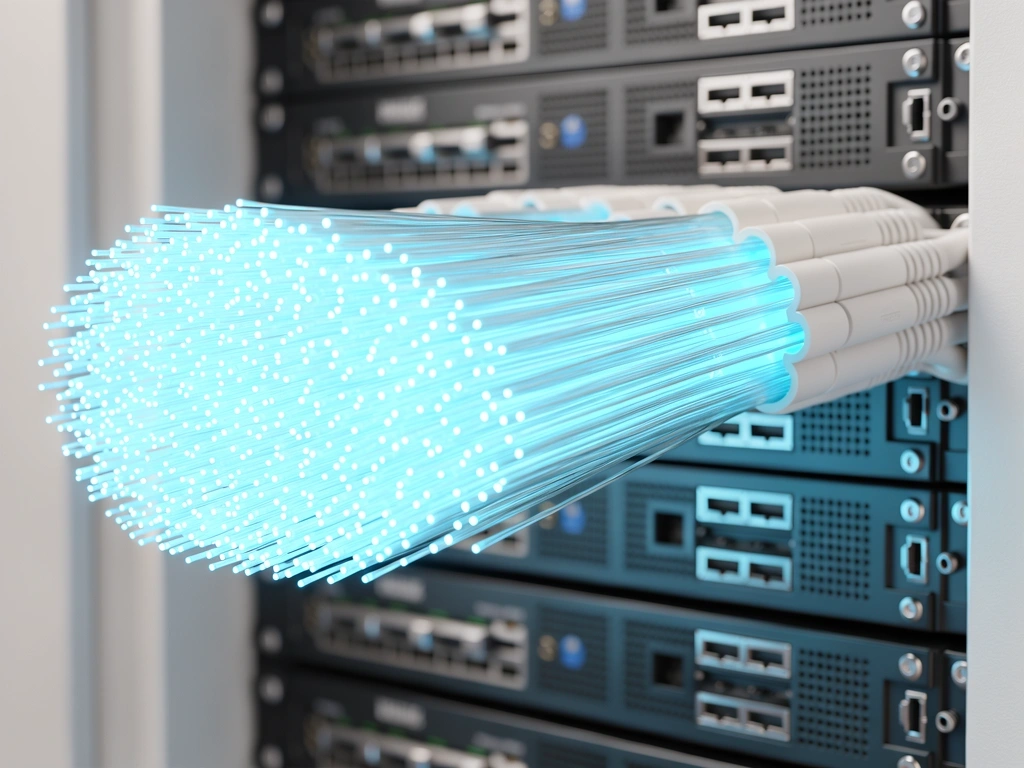
Encryption Protocols
All data in transit is protected by TLS 1.3 or higher. Static data volumes in our core infrastructure utilize AES-256 encryption at rest to prevent unauthorized access.
Access Controls
Human access to unencrypted raw data is restricted to authorized analysts via multi-factor authentication and is logged for auditing purposes at our Hanoi facility.
Subject Rights
You maintain full control over your digital footprint within our systems.
Global Data Flux
As a firm operating in the sphere of global predictive analytics, your data may be processed on secure infrastructure located outside your home jurisdiction. We ensure that such transfers are governed by standard contractual clauses or equivalent legal mechanisms that provide a similar level of protection as your local laws.
We prioritize hosting within regions that maintain high adequacy status for data protection, ensuring your enterprise insights remain shielded regardless of geographic processing location.
Review our Data StandardsInquiries
info@himalayandatapeak.digital
+84 24 3000 0219
Hanoi 19
Mon-Fri: 09:00-18:00